Ryan Maguire’s web page devoted to “The Ghost in the MP3” enlivens a technical feature of MP3/4 formats, compression, with the idea of the ghost, a gothic trope oft-associated (if my past life with literature is serving me well) with the eruption of a suppressed past into perception. As Maguire writes,
“moDernisT” was created by salvaging the sounds and images lost to compression via the MP3 and MP4 codecs. The audio is comprised of lost mp3 compression materials from the song ‘Tom’s Diner’ famously used as one of the main controls in the listening tests to develop the MP3 encoding algorithm. . . . The video is the MP4 ghost of a corresponding video created in collaboration with Takahiro Suzuki. Thus both audio and video are the ‘ghosts’ of their respective compression codecs.”
Because I’ve played around with some musical toys in the past, I think I follow what Maguire is saying about sonic compression. The effect funnels the waveform into a narrower dynamic bandwidth than the original. Peaks reduced, minimal signals magnified. Often, the goal is to create a sense of fullness and consistent presence. Pop music, especially, tends to use compression at multiple points in the recording process. Mastering with sophisticated forms of compression is one reason professional recordings can seem so much bigger or fuller in one’s speakers than your average Garage Band output.
We hear a lot of compressed audio.
But the “ghost” in these machines insisted upon by Maguire invites a social reading of these sources. The season aside, what exactly might be scary about compression? Maguire’s project asks us to consider what may have been lost in our uptake of the MP3. The “Ghost in the MP3” is the something left behind, a sonic detritus that when mixed just so and accompanied by the “corresponding video” (featuring a bug), makes you feel just a bit like you are seeing (and hearing) dead people.
Such a sensation asks us what other felt experience might have been foreclosed by computational processes to which few if any of us recall expressly assenting. [If you did ever assent, of course. Those who have held out with your vinyl all these years, you have my respect.] The raw material of “Ghost in the MP3” is a computational elision, the technical “ghost” we recuperate as aestheticized sensation.
I’d like to consider the word “procedural” in a somewhat similar way. As Maguire exploits polysemic connection with the word “ghost,” and suggests what we may have lost to computational formats, I’d like to consider how our current sense of computational procedurality compares with legal procedurality. Instead of de-synonymizing the meanings gathered round the word “procedure” in different contexts, I’m looking for ways that work with computational procedurality may be seen as relevant, even crucial, to a critical investigation of law, or the ghost thereof.
suggests what we may have lost to computational formats, I’d like to consider how our current sense of computational procedurality compares with legal procedurality. Instead of de-synonymizing the meanings gathered round the word “procedure” in different contexts, I’m looking for ways that work with computational procedurality may be seen as relevant, even crucial, to a critical investigation of law, or the ghost thereof.
In Persuasive Games, Ian Bogost paints procedurality with strokes both manifold and broad. “Procedural rhetoric,” for example, is “the art of persuasion through rule-based representations and interactions rather than the spoken word, writing, images, or moving pictures” (ix). And Bogost nests this procedural rhetoric within a more expansive sense of procedural literacy — “Procedural rhetoric is a type of procedural literacy” (258) — which “entails the ability to reconfigure concepts and rules to understand and process, not just on the computer, but in general” (245). The conceptual fulcrum upon which both definitions turn are “rules.” So true with procedural authorship “of rules of behavior, the construction of dynamic models” (29). The fact that “in computation, those rules are authored in code, through the practice of programming” (29) notwithstanding, “procedurality can . . . entail the operation of cultural, social, and historical systems” (8). In Persuasive Games, “rules” of various kinds are depicted as operating across a range of social processes. Bogost advances the concept as highly transportable across contexts.

What becomes of procedural law in an era of computational procedurality?
Bogost’s writing on procedurality, then, suggests the appropriateness of reconsidering legal procedurality in light of our extant and ongoing work with computational procedurality. Bogost’s nods to rhetoric also present a concept capable of embracing both computational and legal expression. Bogost recounts that Aristotle’s public rhetoric was typically legal rhetoric, yet elaborates his idea of procedural rhetoric through the treatment of mainly non-legal, computational artifacts. Therefore in my following comments I will present notes on my own very basic understanding of procedurality in law and then one possible application of this line of reasoning in a way that enlists some of our current thinking about computation.
According to Legalflip.com, a legal-educational site devoted to “simplifying legal matters”:
Procedural law is a broad term that deals with the rules that the court, lawyers, and parties must follow to properly try a case. In short, procedural laws deal with dates, times, numbers, and other procedural aspects of case that must be met in order for the case to proceed according to the law. Procedural laws are important because they afford parties due process of law under the U.S. Constitution. Due process essentially requires the government to treat individuals fairly under the law.
If you’ve read this far, it may be unnecessary for me to point out that this definition of legal procedurality emphasizes, again, rules. The stakes here, of course, are quite different than those in gaming contexts. Yet there is still the possibility of reading even everyday legal procedures for their metonymic relation to their governmental surround. As law professor Paul MacMahon notes in “Proceduralism, Civil Justice, and American Legal Thought,” discussions of “civil procedure” present “any reasonably competent American law professor” with “a vehicle for exploring questions of state sovereignty” (563).
MacMahon uses the substance/procedure dichotomy to further clarify the nature of legal procedurality. Substance seems to be what you are aiming for with a law, procedure the way to get there.
A procedure is a way of doing something. In law, procedure is a way of ‘doing’ substantive law. Substantive law is the body of rules that purports to guide people’s conduct outside litigation and the lawmaking process . . . Substantive due process . . . prevents government actors from depriving persons of certain interests, no matter how they do it. Procedural due process doctrine regulates only how governments deprive a person of life, liberty, or property. (555)
* * *
With these definitions of procedurality in mind, I’ve been working through The Drone Papers. They are published by the Intercept, an online source of investigative news featuring journalists like Glenn Greenwald (who broke the story on our NSA’s collection of US cell phone metadata) and Jeremy Scahill (author of Blackwater: The Rise of the World’s Most Powerful Mercenary Army).

“A Yemeni boy walks past a mural depicting a U.S. drone on December 13 [2013] in the capital Sanaa.” cnn.com
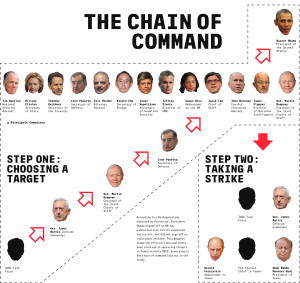
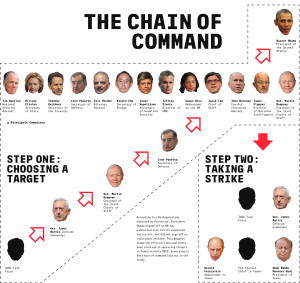
For many years, lawyers and human rights advocates have wondered about the chain of command. How are non-battlefield assassinations authorized? Does it fall within the Authorization for Use of Military Force (AUMF), or through some other authority? The documents we have are not comprehensive, but they suggest a linear chain—all the way up to the president of the United States (POTUS).
The government source providing these documents “said he decided to provide these documents to The Intercept because he believes the public has a right to understand the process by which people are placed on kill lists and ultimately assassinated on orders from the highest echelons of the U.S. government” (Scahill). Already, I find myself noting language requiring “decoding” and a “process” by which state violence is created in the style of legal procedure. The Intercept’s current find responds to our government’s determined effort to keep the actual process opaque:
The first drone strike outside of a declared war zone was conducted more than 12 years ago, yet it was not until May 2013 that the White House released a set of standards and procedures for conducting such strikes. Those guidelines offered little specificity, asserting that the U.S. would only conduct a lethal strike outside of an “area of active hostilities” if a target represents a “continuing, imminent threat to U.S. persons,” without providing any sense of the internal process used to determine whether a suspect should be killed without being indicted or tried.
from The Intercept “Drone Papers”
Perhaps a glance at the Intercept’s findings will convince you that this is a matter that might be aptly explored with critical legal rhetoric. But I’d like to add that computation enables the entire process. Unmanned aircraft couldn’t be flown without it.

In addition, the intelligence used to profile victims and ultimately try to kill them is largely the work of computational technology as well. Noting “the poverty of signals intelligence,” Begley writes: “With limited ability to conduct raids or seize materials from targeted individuals in Yemen and Somalia, JSOC [Joint Special Operations Command] relied overwhelmingly on monitoring electronic communications to discover and ultimately locate targets” (A Visual Glossary).
The ongoing backdrop of computational communicative processes on a world scale is what allows our Drone Wars to continue. This contextualizes the NSA’s collection of our domestic meta-data; we are living through a US-led militarization and weaponization of personal data on a global scale. As Begley explains:

“Hellfire missiles—the explosives fired from drones—are not always fired at people. In fact, most drone strikes are aimed at phones. The SIM card provides a person’s location—when turned on, a phone can become a deadly proxy for the individual being hunted.”
“When a night raid or drone strike successfully neutralizes a target’s phone, operators call that a ‘touchdown.'”
The Drone Papers of course touch upon the inaccuracy of drone strikes and the willingness of their operators to accept high rates of human collateral damage — but I’ll assume all of you are already aware of these grim realities.
* * *
In closing: If Bogost is right, that we can learn something fundamental about the nature of our society by examining the way computational systems enact their procedurality —
If procedural literacy can have implications beyond reading video games–
If the affordances of computation present states with capacities that outstrip the traditional constraints of legal procedurality —
If our drone warfare program yokes the capacities of computation to essentially an extra-judicial procedurality–
What might be revealed through a procedural-rhetorical reading of the sources on offer in The Drone Papers?
 Mariolina Salvatori (formerly of Pitt English) I’m willing to encounter this cognitive-affective state. I would note, however, that the seminal Elements and Pleasures of Difficulty turned on transmuting interpretive difficulty into generative writing, included no computational examples. Perhaps the transposition of this concept to code-based learning merits more explicit theorization.
Mariolina Salvatori (formerly of Pitt English) I’m willing to encounter this cognitive-affective state. I would note, however, that the seminal Elements and Pleasures of Difficulty turned on transmuting interpretive difficulty into generative writing, included no computational examples. Perhaps the transposition of this concept to code-based learning merits more explicit theorization.
 suggests what we may have lost to computational formats, I’d like to consider how our current sense of computational procedurality compares with legal
suggests what we may have lost to computational formats, I’d like to consider how our current sense of computational procedurality compares with legal 



 I was struck by the way in which he did several things at once. Sure, he helped us follow a functional arc of code rooted in libraries and the sine qua non of digitalia, copy/paste. And boy did he define a host of terms, such as API and ASCII and Unicode, while leaving some opaque (such as “web scraping”). But he also unfolded bits of “brogrammer” lore (his word) and touched upon points of cultural critique, such as the corporate desire to index our online avatars to our consumptive bodies.
I was struck by the way in which he did several things at once. Sure, he helped us follow a functional arc of code rooted in libraries and the sine qua non of digitalia, copy/paste. And boy did he define a host of terms, such as API and ASCII and Unicode, while leaving some opaque (such as “web scraping”). But he also unfolded bits of “brogrammer” lore (his word) and touched upon points of cultural critique, such as the corporate desire to index our online avatars to our consumptive bodies. He reminded me of a foreign language instructor with whom I am currently taking a class (beginning Turkish). She shows us with infinite patience how a difficult yet extremely regular grammar functions at a code-like level, and intersperses this work with cultural asides in rapid-fire frames. In both cases I see a translation from semiotic domain to semiotic domain, to use a term from Gee’s What Video Games Have to Teach Us About Learning and Literacy. Critical learning, Gee claims, is a matter of both internal and external design grammars — both the content within the design space afforded by a given domain, and the ways of thinking, acting, and being that constitute that domain in the social sense (which many of us felt was spottily addressed by Bogost’s Persuasive Games).
He reminded me of a foreign language instructor with whom I am currently taking a class (beginning Turkish). She shows us with infinite patience how a difficult yet extremely regular grammar functions at a code-like level, and intersperses this work with cultural asides in rapid-fire frames. In both cases I see a translation from semiotic domain to semiotic domain, to use a term from Gee’s What Video Games Have to Teach Us About Learning and Literacy. Critical learning, Gee claims, is a matter of both internal and external design grammars — both the content within the design space afforded by a given domain, and the ways of thinking, acting, and being that constitute that domain in the social sense (which many of us felt was spottily addressed by Bogost’s Persuasive Games). instruction, the chance to ask questions, the comestible goldfish. Even so, I felt able to grasp some of the contours of what we were doing. I wasn’t just copying & pasting blindly, but instead thinking about the shareable nature of Python code, the value of open source libraries, and how so much of the latticed software constituting my humble bots is out there, above the virtual
instruction, the chance to ask questions, the comestible goldfish. Even so, I felt able to grasp some of the contours of what we were doing. I wasn’t just copying & pasting blindly, but instead thinking about the shareable nature of Python code, the value of open source libraries, and how so much of the latticed software constituting my humble bots is out there, above the virtual 



 No, no. It’s “raw input” that let’s you really do stuff with python. It establishes a real-time relationship between the code being manipulated within the editor and the output of the console.
No, no. It’s “raw input” that let’s you really do stuff with python. It establishes a real-time relationship between the code being manipulated within the editor and the output of the console.
